Cybersecurity & Data Privacy
For the Rest of Us
Cybersecurity compliance platform for growing businesses.
Get a live security score, a clear data privacy roadmap, and a unified GRC platform — without hiring a full-time CISO.
From Chaos to Peace of Mind
Most Small and Mid-Sized Companies Don't Lack Security Tools. They Lack Structure!
The Risk of Inaction
Without a system, you are taking a risk. One breach could be fatal! A simple, legal request from your regulators, customers or employes can become a big costly liability
- Constant Worry: Did we patch that? Did everyone sign the policy?
- Scrambling for Audits: Manual evidence gathering takes weeks, if the data even exists.
- Silent Vulnerabilities: We don't do independent testing so we don't know what we don't know.
- No budget: Only large companies can afford to do it.
- No knowledge: Internal teams do not have the expertise.
Complete Peace of Mind
We provide the plans, the platform automates the work. You sleep well knowing your compliance is active, documented, and proven.
- Crystal Clear Policies: Who does what, when, and with a track record.
- Always Audit-Ready: All important decisions and data points are captured and organized.
- Independent Penetration Testing: Top of the line Penetration Testing tools available to tame vulnerabilities.
- Trust & Growth: A small investment helps you win trust and grow your business.
- Recipes and Automation: Our platform guides your team on the path to cybersecurity and data privacy safety.
If your company collects customer or employee data, you are subject to cybersecurity risk and data privacy obligations.
→ When ransomware hits.
→ When regulators ask questions.
→ When cyber insurance providers request proof of controls.
→ When enterprise clients send detailed security questionnaires.
Without a centralized cybersecurity compliance system, response becomes stressful, slow, and expensive.
What growing companies need isn't more tools. They need visibility, prioritization, and a structured GRC platform built specifically for SMBs.
Why Choose CyberSafePath?
This platform was created by a team of cybersecurity experts.
Their combined expertise includes:
- ✓ Managing GDPR, PIPEDA, HIPAA, ISO and SOC-regulated environments
- ✓ Leading audit readiness initiatives
- ✓ Responding to ransomware and data breaches
- ✓ Overseeing disaster recovery programs
- ✓ Handling data breach litigation exposure
- ✓ Securing and renewing cyber insurance coverage
Most cybersecurity compliance software is built for enterprises with full-time compliance teams.
Most consultants provide static reports without ongoing visibility.
This platform delivers something different:
A practical Virtual CISO solution for growing companies.

How the Cybersecurity Compliance Platform Works
Consolidated into a single, automated platform for Policies, Risk, Training, and Data Privacy.
Instant Cybersecurity Assessment
Your administrator logs in and receives:
- ✓ A live cybersecurity score
- ✓ A structured compliance roadmap
- ✓ A prioritized risk mitigation plan
You immediately understand your company's current posture.
Employee Security Awareness & Policy Management
Employees complete:
- ✓ Cybersecurity and data privacy training modules
- ✓ Knowledge validation quizzes
- ✓ Electronic policy acknowledgments
All actions are logged automatically for audit readiness.
This reduces human risk — the leading cause of security incidents.
Risk Management & Compliance Tracking
Manage:
- ✓ Risk registries
- ✓ Vendor risk exposure
- ✓ Asset oversight
- ✓ Data privacy controls
Your dashboard updates in real time.
You gain a single pane of glass across your entire cybersecurity and compliance program.

More about Training
Key Benefit: Enhanced security and automation.
Get a hacker's perspective on your web apps, network, and cloud
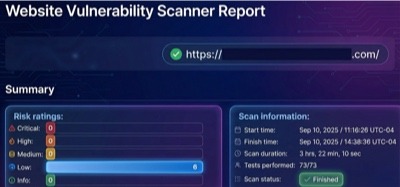
More about Vulnerability Scanning
1. Attack surface mapping and recon
Powerful scanners for mapping exposed network assets, api and web apps: open ports, running services, OS. Great for extracting Insights from subdomains, outdated technologies, reverse DNS, WAFs, and hidden files
2. Vulnerability exploitation
Automatic exploitation of old and new, critical CVEs, SQL injection, XSS and more. Evidence-rich results: screenshots, network maps, exploit paths, local users, running processes, and traffic logs
3. Network & cloud vulnerability scanning
Network Vulnerability Scanner that combines 4 detection engines to ensure comprehensive technology coverage
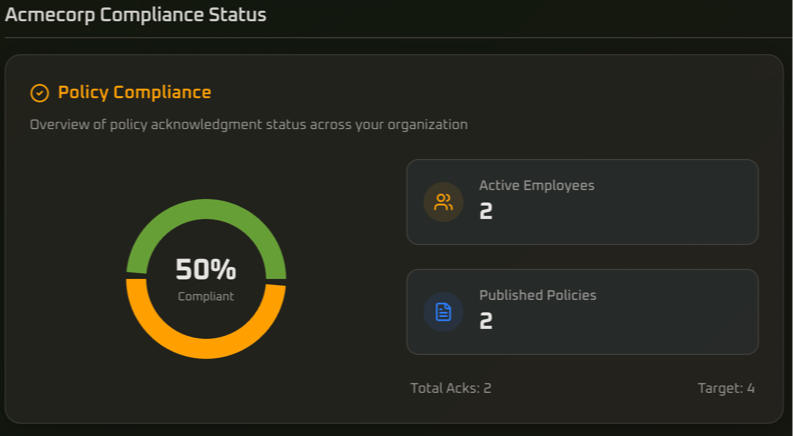
More about Compliance Audit
- Individual Employee Scores
- Agregated Company score for managers
- Automated and Manual Reports
- Up to 2 years retention
- Reports for managers on Policy acknowlegement and Training progress.

More about Automated Policies
- CyberSafePath provides industry standard templates
- Customize or upload your own and publish to the entire company
- Track change control for compliance
- Let your employees read and acknowledge the policies
More about Reporting
Single Pane of Glass for IT Admins
- Track entire cybersecurity posture
- Aggregated & per-employee scores (Compliance, Training)
- Risk scores from Risk & Data registries
- Budget prioritization based on actionable risk reduction

More about Vendor Management
- Add your list of vendors manually or populate our template file
- Change the default info to suit your business
- Maintain records of Risk, Contacts, and Responsibilities
- Store compliance evidence (certifications, documents)
- Generate and send tailored Security Surveys

More about Asset Inventory
- Access to recent activity and what assets, accessories, consumables you have
- Checked in, checked out, recently updated or deleted items
- Quick access to license and multi-pack licenses assignment
- Email alerts when your licenses are expiring
- Asset Checkout/Checkin notifications
- Checkin Deadline Approaching notifications
Designed for Audit Readiness and Cyber Insurance Compliance
Not promises. Proof!
Growing companies increasingly face:
- →Stricter data privacy regulations
- →Insurance carrier underwriting scrutiny
- →Client-mandated security reviews
- →Investor and due diligence cybersecurity assessments
This platform ensures you can demonstrate:
- ✓Documented policies
- ✓Employee training completion
- ✓Risk mitigation progress
- ✓Structured governance oversight
How Vulnerable Are You?
Most SMBs don't know they are exposed until it's too late. Get a personalized report in 5 minutes.
You'll receive:
- ✓ A snapshot of your cybersecurity and compliance posture
- ✓ A prioritized risk reduction roadmap
- ✓ Clear next steps tailored to your organization
Even if you never become a customer, you'll gain clarity.
And clarity is the foundation of cybersecurity maturity.
Simple, Transparent Pricing
Choose the plan that fits your scale.
- 10 Licenses
- Priority Email Support
- API Access
- 5 Policies
- 20 Licenses
- SSO Integration
- 1-Year Log Retention
- Daily Scans
- 50 Licenses
- Phone Support
- Custom Branding
- 2-Year Log Retention
- Unlimited Licenses
- Dedicated CSM
- SOC2 Reports
- Custom Domain
Is This the Right Fit?
We are purpose-built for growing businesses that need structure — not bureaucracy.
This is for you if one of the following applies:
- You operate a digital-first business
- You collect customer or employee data
- You lack a dedicated cybersecurity or compliance team
- You need audit-ready documentation
- You want structured risk management without enterprise complexity
This is not for you if:
- You already maintain a large in-house security team
- You require advanced enterprise certifications with complex integrations
- You operate with a seven-figure compliance budget
- You are looking for a quick fix, not stepping on a path to safety
- You are a cyber target of a nation-state
About Us
43%
of cyber attacks target small businesses.
90%
of security tools are built only for Enterprise.
Built for the rest of us.
We founded CyberSafePath with the goal of making security a right, not a luxury.
After decades helping companies of all sizes, we know intimately that the 20/80 rule applies to cybersecurity as well: 20% of effort will give you 80% of the results.
CyberSafePath skips all the lengthy discovery and interviews tricks, and gives you tools and advice out of the box.
Frequently Asked Questions
Everything you need to know about the platform.